Even as the controversy surrounding Harvard’s secret searches of staff members’ email accounts deepens, an examination of Stanford’s privacy policies suggests that such a controversy may be precluded by severe limitations on the information and account access afforded to University administrators.
Stanford’s Internet Privacy Policy
By registering on Stanford’s network, computer users allow Academic Computing Services (ACS) to collect basic information about their devices, including make and model, IP addresses, operating systems and hardware addresses.
ACS also collects personal information from network users, including phone numbers, email addresses and residential information. According to ACS, this data is used primarily to provide technical support or generate statistics about device trends, which inform policy and user support decisions.
Access to information collected by ACS is restricted to employees who are involved with user support, and no personally identifiable information is shared outside the University unless it is requested by court order, subpoena or emergency circumstances.
Brad Hayward, senior director for strategic communications, wrote in a statement to The Daily that Stanford “does not monitor individual student or employee email or Internet usage in any ongoing way.”
According to Hayward, only Tina Darmohray, chief information security officer, can authorize a review of user information. Hayward said that these reviews are done in consultation with the Office of General Counsel to “fully ensure the appropriate practices are followed.”
Hayward emphasized that the University “only accesses information in response to a situation that truly demands it,” adding that these situations arise very infrequently. According to Hayward, whether or not an individual is notified before their information is accessed depends largely on the situation.
“If a member of the University community went missing for an extended period and there was a serious safety concern for that individual, or if an investigation was underway with respect to employee fraud or misuse of funds, it obviously would not be feasible to provide notice to the individual involved,” Hayward said.
However, Hayward said that if a student or faculty member’s information were the subject of a subpoena, the University would offer notice before accessing the information.
Ryan Globus ’14, a Residential Computer Consultant (RCC) in Florence Moore West, said that RCCs also have limited access to student information.
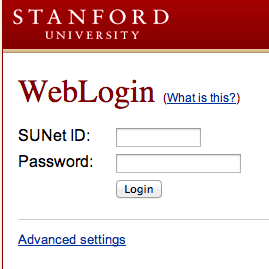
According to Globus, RCCs can view the types of electronic devices registered to each network user, as well as the IP addresses, phone numbers, SUNet IDs and room numbers of the users.
“We’re only allowed to use those for RCC purposes, and we’re allowed to disclose them to other RCCs for our RCC purposes,” he said. “If there’s any violation of that, we get fired.”
Concerns with Google Apps
Aleecia McDonald, director of privacy at the Center for Internet and Society at Stanford Law School, expressed general satisfaction with Stanford’s Internet privacy policies, noting that some universities monitor traffic to certain sites or limit bandwidth to limit incidents of online piracy.
“Of the academic policies I’m familiar with, [Stanford’s policy] strikes a reasonable balance between the University and the people using university facilities,” McDonald said. “There are a number of universities more restrictive than Stanford.”
However, McDonald did express reservations about Stanford’s use of Google Apps, which IT Services began using in January 2012.
Currently, both Stanford and Google’s privacy policies cover the Gmail, Google Calendar and Google Docs applications. All other Google applications are covered only by Google’s privacy policy and terms of use.
In addition to basic personal information that users share when they create Google accounts, Google also collects search queries and device information like IP addresses, and records location information gathered from GPS signals, cell towers and sensor data from wifi access points.
Google has come under fire recently for working around privacy settings in Apple’s Safari browser to track browser users for advertising purposes, and also drew criticism after utilizing Gmail user data in behavioral advertising.
McDonald said that she is not comfortable with storing her calendar or email information on Google’s servers because she makes “strong promises” to subjects in her research to keep their information confidential.
“If I have human subjects’ data and it’s personally identifiable in some way, I’ve made pledges that that data will not get reused for other purposes,” she said. “I can’t know that I can uphold those promises forever if Google has the data. They can change their policies at any time.”
According to McDonald, many universities use services like Google for email to avoid the expense of hosting their own servers and securing their networks against hackers.
“Rather than hiring more staff to deal with security, it’s less money for universities to just hand off their infrastructure to Google and let Google take care of it,” she said.
However, McDonald acknowledged the many competing factors that contribute to the development of the University’s privacy policy, and said that a perfect privacy policy would be extremely difficult to achieve.
“Is it ideal for the financial aspects of the University? Is it ideal for protecting the privacy of the individuals? Is it ideal for intellectual property protection?” she said. “These are all valid things to want, but it might be impossible to get all three perfectly at the same time.”